decrypt nfc tag Amiibo data are stored on the physical Amiibo as a .bin file. .Bin file - raw data from physical Amiibo. .NFC file - the file needed to write to an NFC tag/card or send via nfc to your switch, . Near Field Communication (NFC) is used all and everywhere. As it stands there are over two billion NFC-enabled devices (many of them smartphones) in use today. This basically means over 20% of the .
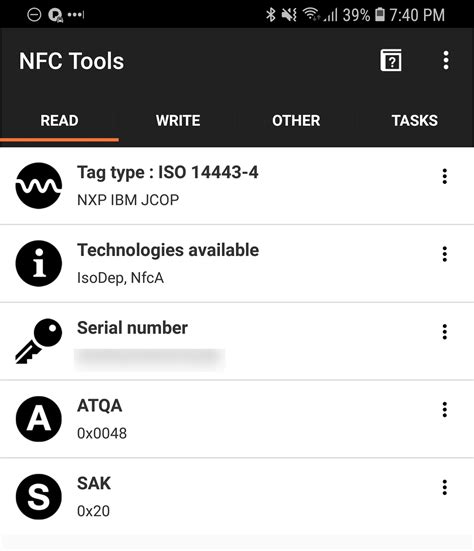
0 · copy a tag ISO 14443
1 · Sławomir Jasek
2 · Step
3 · Read/write to NFC tag with password protection
4 · Hacking MIFARE & RFID
5 · GitHub
6 · Encrypted RFID & NFC tags
7 · Decrypting and Emulating Mifare 1K Cards using the RFID Tools
8 · Bambu
What is the maximum power an NFC-enabled card can draw from a contactless payment terminal? What are the determinants (i.e. card reader .
Some tags such as MIFARE DESFire natively support passwords / encryption as you describe. Recreating this functionality on the more common types of tags (Topaz/MIFARE .Amiibo data are stored on the physical Amiibo as a .bin file. .Bin file - raw data from physical Amiibo. .NFC file - the file needed to write to an NFC tag/card or send via nfc to your switch, .
This tool provides several features to interact with (and only with) MIFARE Classic RFID-Tags. It is designed for users who have at least basic familiarity with the MIFARE Classic technology. . NFC was created as a new way of communicating with other RFID tags. NFCs main purpose was to break out of the standard tag/reader “read-only” pattern. This is to allow . Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise .If you have an Android phone with NFC, you could try using Mifare Classic Tool to read the card with the key files that are included. If the tag uses default/weak/common keys, you might be .
copy a tag ISO 14443
The Proxmark3 RDV4 makes quick work of decyphering and emulating Mifare classic cards, and with the Blue Shark bluetooth module and RFID Tools App, you can take your entire lab into .All radio frequency data transmission between the tag and reader is encrypted using a secure algorithm. By using industry standard encryption techniques, iCLASS reduces the risk of .You can decrypt millions of RFID tag encryptions and NFC encryptions without filling up storage space on a smart phone or OEM scanning device. Additionally, since Microtrace’s encrypted .
buy passive rfid tags
If you have a Proxmark3 (or other RFID debugging tool), you can sniff and decrypt the contents of your tags and submit them for review. The more data we have, the easier it is to compare differences to learn what each byte represents. Some tags such as MIFARE DESFire natively support passwords / encryption as you describe. Recreating this functionality on the more common types of tags (Topaz/MIFARE Ultralight, etc.) is inherently impossible as NFC tags do not have built in protections for the copying of their data (by design).Amiibo data are stored on the physical Amiibo as a .bin file. .Bin file - raw data from physical Amiibo. .NFC file - the file needed to write to an NFC tag/card or send via nfc to your switch, this emulates a physical Amiibo.This tool provides several features to interact with (and only with) MIFARE Classic RFID-Tags. It is designed for users who have at least basic familiarity with the MIFARE Classic technology. You also need an understanding of the hexadecimal number system, because all data input and output is in hexadecimal.
Sławomir Jasek
NTAG 2xx incl. the NTAG I2C fall under the NFC-A category, whereas NTAG5 ICs fall under the NFC-V Technology. On top, e.g. NTAG 21x ICs support the Get_Version Command (60h) that will give back the major and minor product versions, as well as the memory size. NFC does not by default need any special NXP authentication. See the StickyNotes app at http://nfc.android.com. NFC was created as a new way of communicating with other RFID tags. NFCs main purpose was to break out of the standard tag/reader “read-only” pattern. This is to allow both devices to become reader, antenna, and tag.
Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise the security of a company if they are using these types of cards. If you have an Android phone with NFC, you could try using Mifare Classic Tool to read the card with the key files that are included. If the tag uses default/weak/common keys, you might be able to decrypt the whole tag right there.
The Proxmark3 RDV4 makes quick work of decyphering and emulating Mifare classic cards, and with the Blue Shark bluetooth module and RFID Tools App, you can take your entire lab into the field with total discretion.If you have a Proxmark3 (or other RFID debugging tool), you can sniff and decrypt the contents of your tags and submit them for review. The more data we have, the easier it is to compare differences to learn what each byte represents.
Some tags such as MIFARE DESFire natively support passwords / encryption as you describe. Recreating this functionality on the more common types of tags (Topaz/MIFARE Ultralight, etc.) is inherently impossible as NFC tags do not have built in protections for the copying of their data (by design).
Amiibo data are stored on the physical Amiibo as a .bin file. .Bin file - raw data from physical Amiibo. .NFC file - the file needed to write to an NFC tag/card or send via nfc to your switch, this emulates a physical Amiibo.
This tool provides several features to interact with (and only with) MIFARE Classic RFID-Tags. It is designed for users who have at least basic familiarity with the MIFARE Classic technology. You also need an understanding of the hexadecimal number system, because all data input and output is in hexadecimal.
NTAG 2xx incl. the NTAG I2C fall under the NFC-A category, whereas NTAG5 ICs fall under the NFC-V Technology. On top, e.g. NTAG 21x ICs support the Get_Version Command (60h) that will give back the major and minor product versions, as well as the memory size. NFC does not by default need any special NXP authentication. See the StickyNotes app at http://nfc.android.com. NFC was created as a new way of communicating with other RFID tags. NFCs main purpose was to break out of the standard tag/reader “read-only” pattern. This is to allow both devices to become reader, antenna, and tag. Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise the security of a company if they are using these types of cards.
can my phone read rfid tags
If you have an Android phone with NFC, you could try using Mifare Classic Tool to read the card with the key files that are included. If the tag uses default/weak/common keys, you might be able to decrypt the whole tag right there.
Step
can a smartphone read rfid
bluetooth rfid reader writer
$29.14
decrypt nfc tag|GitHub