smart card cryptographic log This article explains tools and services that smart card developers can use to help identify certificate issues with the smart card deployment. Debugging and tracing smart card . The (un)official home of #teampixel and the #madebygoogle lineup on Reddit. Get support, .
0 · microsoft enhanced cryptographic provider
1 · microsoft enhanced cryptographic certificate
2 · microsoft cryptographic services
3 · microsoft cryptographic service provider certificate
4 · microsoft cryptographic providers
5 · microsoft cryptographic keys
6 · microsoft cryptographic key storage
Desktop readers ID CPR40.30- are designed for contactless data exchange & ideal for .
Each smart card must have a Cryptographic Service Provider (CSP) that uses the CryptoAPI interfaces to enable cryptographic operations, and the WinSCard APIs to enable . This article explains tools and services that smart card developers can use to help identify certificate issues with the smart card deployment. Debugging and tracing smart card . Modern Microsoft cryptography providers. Comparison of modern Microsoft providers. Legacy Microsoft cryptography providers. Providers still used out of the box, but are . From microsoft documentation. In steps 6 and 7 (Kerberos SSP <-> CSP or Base CSP): In essence, it exchanges a copy of the x.509 certificate (from a smart card) in the pre-authentication data field of the request and is .
microsoft enhanced cryptographic provider
microsoft enhanced cryptographic certificate
The Smart Card Alliance is a not-for-profit, multi-industry association working to stimulate the understanding, adoption, use and widespread application of smart card technology. The TPM can also be used to generate and store cryptographic keys. Additionally, cryptographic operations using these keys take place on the TPM preventing the private keys .
If you don't want to read straight from standards, and you are looking something in book form, this is a nice primer, (fairly) entry level into smart card security: .
Due to a limitation with the legacy CSP, the Microsoft Base Smart Card Crypto Provider will not see any ECC certificates or keys. To view ECC certificate and key information, use the Smart .
By utilizing Trusted Platform Module (TPM) devices that provide the same cryptographic capabilities as physical smart cards, virtual smart cards accomplish the three . This article for IT professionals and smart card developers describes the Group Policy settings, registry key settings, local security policy settings, and credential delegation policy settings that are available for configuring smart cards. Each smart card must have a Cryptographic Service Provider (CSP) that uses the CryptoAPI interfaces to enable cryptographic operations, and the WinSCard APIs to enable communications with smart card hardware.
This article explains tools and services that smart card developers can use to help identify certificate issues with the smart card deployment. Debugging and tracing smart card issues requires a variety of tools and approaches.
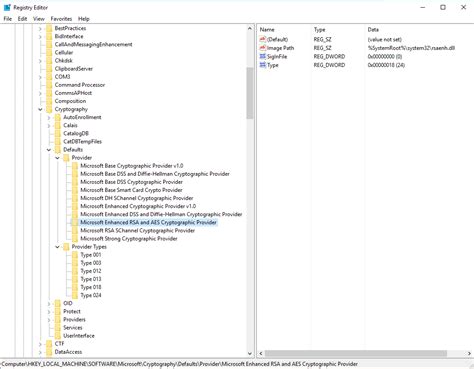
Modern Microsoft cryptography providers. Comparison of modern Microsoft providers. Legacy Microsoft cryptography providers. Providers still used out of the box, but are limited in abilities are generally not used. Deprecated Microsoft cryptography providers. From microsoft documentation. In steps 6 and 7 (Kerberos SSP <-> CSP or Base CSP): In essence, it exchanges a copy of the x.509 certificate (from a smart card) in the pre-authentication data field of the request and is signed by the private key.The Smart Card Alliance is a not-for-profit, multi-industry association working to stimulate the understanding, adoption, use and widespread application of smart card technology. The TPM can also be used to generate and store cryptographic keys. Additionally, cryptographic operations using these keys take place on the TPM preventing the private keys of certificates from being accessed outside the TPM.
If you don't want to read straight from standards, and you are looking something in book form, this is a nice primer, (fairly) entry level into smart card security: http://www.amazon.com/Smart-Cards-Tokens-Security-Applications/dp/1441944265 .Due to a limitation with the legacy CSP, the Microsoft Base Smart Card Crypto Provider will not see any ECC certificates or keys. To view ECC certificate and key information, use the Smart Card Key Storage Provider: certutil -csp "Microsoft Smart Card Key Storage Provider" By utilizing Trusted Platform Module (TPM) devices that provide the same cryptographic capabilities as physical smart cards, virtual smart cards accomplish the three key properties that are desired by smart cards: nonexportability, isolated cryptography, and .
microsoft cryptographic services
This article for IT professionals and smart card developers describes the Group Policy settings, registry key settings, local security policy settings, and credential delegation policy settings that are available for configuring smart cards.
Each smart card must have a Cryptographic Service Provider (CSP) that uses the CryptoAPI interfaces to enable cryptographic operations, and the WinSCard APIs to enable communications with smart card hardware. This article explains tools and services that smart card developers can use to help identify certificate issues with the smart card deployment. Debugging and tracing smart card issues requires a variety of tools and approaches.
Modern Microsoft cryptography providers. Comparison of modern Microsoft providers. Legacy Microsoft cryptography providers. Providers still used out of the box, but are limited in abilities are generally not used. Deprecated Microsoft cryptography providers.
From microsoft documentation. In steps 6 and 7 (Kerberos SSP <-> CSP or Base CSP): In essence, it exchanges a copy of the x.509 certificate (from a smart card) in the pre-authentication data field of the request and is signed by the private key.The Smart Card Alliance is a not-for-profit, multi-industry association working to stimulate the understanding, adoption, use and widespread application of smart card technology. The TPM can also be used to generate and store cryptographic keys. Additionally, cryptographic operations using these keys take place on the TPM preventing the private keys of certificates from being accessed outside the TPM. If you don't want to read straight from standards, and you are looking something in book form, this is a nice primer, (fairly) entry level into smart card security: http://www.amazon.com/Smart-Cards-Tokens-Security-Applications/dp/1441944265 .
Due to a limitation with the legacy CSP, the Microsoft Base Smart Card Crypto Provider will not see any ECC certificates or keys. To view ECC certificate and key information, use the Smart Card Key Storage Provider: certutil -csp "Microsoft Smart Card Key Storage Provider"
How Does an NFC Tag Reader Work? The technology behind NFC tag readers .
smart card cryptographic log|microsoft cryptographic key storage