smart card network authentication This Personal Identity Verification (PIV) 101 is intended to help you understand the purpose and uses of a PIV credential at your organization. This PIV 101 focuses on using PIV credentials for logical access such as authenticating to networks or . $29.99
0 · smart card multi factor authentication
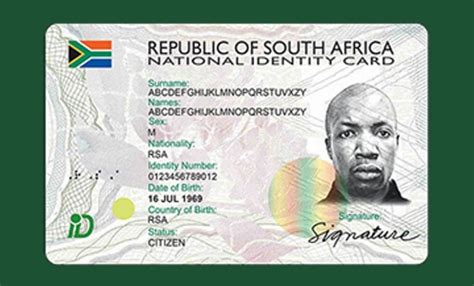
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
Around the Promoted by Taboola. Get the latest 2024 NFL Playoff Picture seeds and scenarios. See the full NFL conference standings and wild card teams as if the season ended .
This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS .How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
nfc opensense tm tags
This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.This Personal Identity Verification (PIV) 101 is intended to help you understand the purpose and uses of a PIV credential at your organization. This PIV 101 focuses on using PIV credentials for logical access such as authenticating to networks or .
Give smart cards to approved users and help them turn on the cards, choose a secret code, and use the cards properly. Provide classes and help for users to learn about smart card logins and get answers to questions or worries.
nexus 6p nfc tags
Introduction. These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on . Password-based authentication is the most common and simplest method of authentication for securing your network monitoring program. Here, the "password" might be a username-password combination, passcode, or PIN. It's intuitive, as many users are already familiar with such login methods.Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.
nfc price tag
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.This article contains configuration information specific to the following authentication methods in EAP. EAP-Transport Layer Security (EAP-TLS): Standards-based EAP method that uses TLS with certificates for mutual authentication. Appears .Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.This Personal Identity Verification (PIV) 101 is intended to help you understand the purpose and uses of a PIV credential at your organization. This PIV 101 focuses on using PIV credentials for logical access such as authenticating to networks or .
Give smart cards to approved users and help them turn on the cards, choose a secret code, and use the cards properly. Provide classes and help for users to learn about smart card logins and get answers to questions or worries.
Introduction. These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on .

Password-based authentication is the most common and simplest method of authentication for securing your network monitoring program. Here, the "password" might be a username-password combination, passcode, or PIN. It's intuitive, as many users are already familiar with such login methods.Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.
smart card multi factor authentication
smart card identity
Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.
smart card based identification system
nfc payment tag
nfc barcode tag
1. Yes, you can write-protect (most) tags, which inhibits others from overwriting your content. If .
smart card network authentication|smart card based identification system